Eliminate Payment Fraud caused by Vendor Email Compromise (VEC)
THE PROBLEM
When Trusted Vendors Become the Threat
Vendor Email Compromise (VEC) attacks are on the rise, using hijacked vendor accounts to send fraudulent invoices and payment requests.

THE CHALLENGE
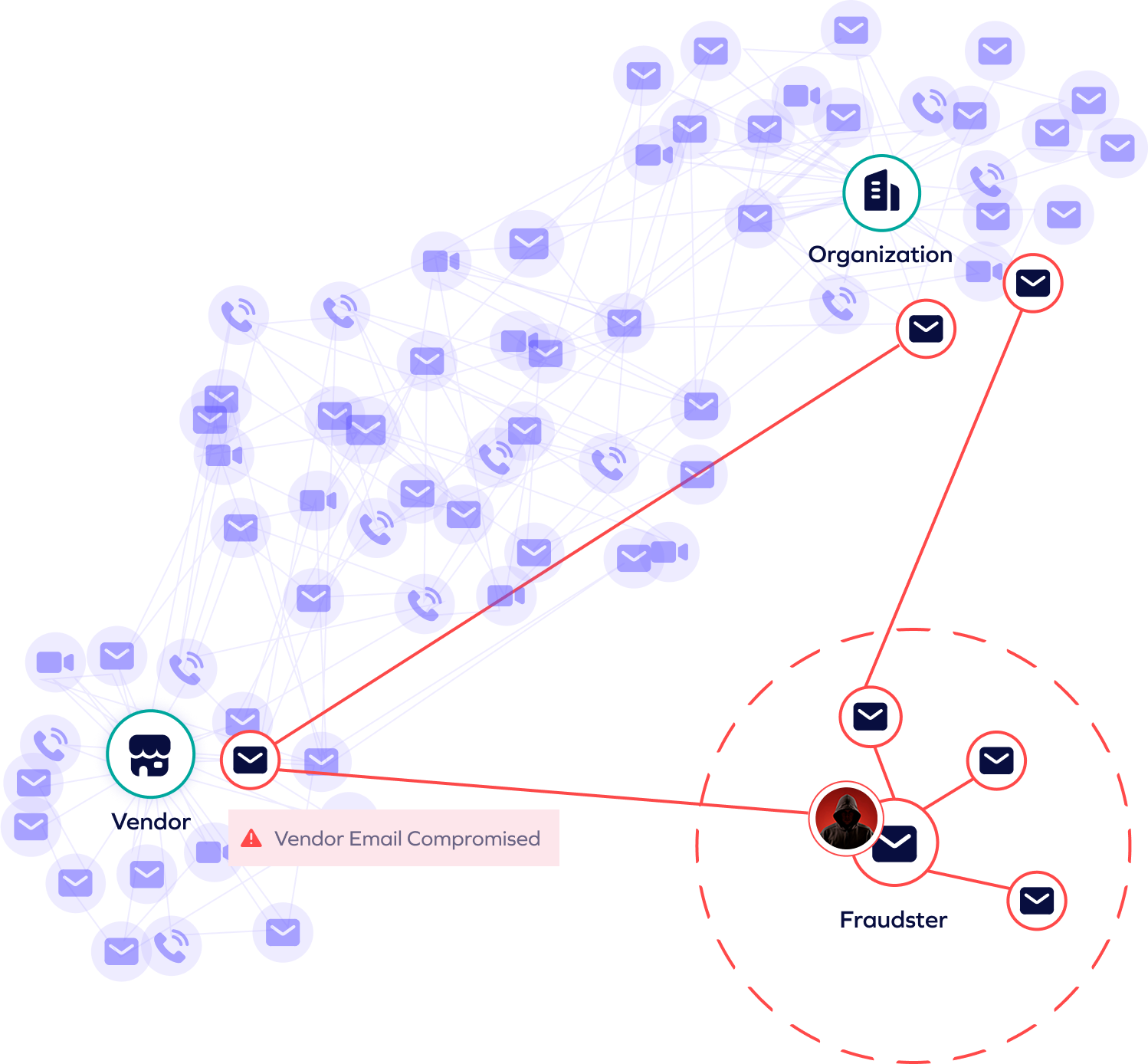
Attackers hijack vendor email accounts to send fraudulent payment requests, bypassing traditional email security and behavioral AI models that fail to detect compromised vendors. These attacks blend seamlessly into legitimate business communications, making them nearly undetectable.
After weeks or even months of research, attackers analyze vendor-client relationships, billing cycles, and financial processes to craft highly targeted, convincing requests. Their deep understanding of business operations allows them to manipulate employees into processing fraudulent payments.
VEC attacks avoid malware and malicious links, relying instead on well-crafted text-based requests that evade detection. With no obvious indicators of compromise, these scams slip past conventional security tools, leaving businesses vulnerable to financial losses.
THE SOLUTION
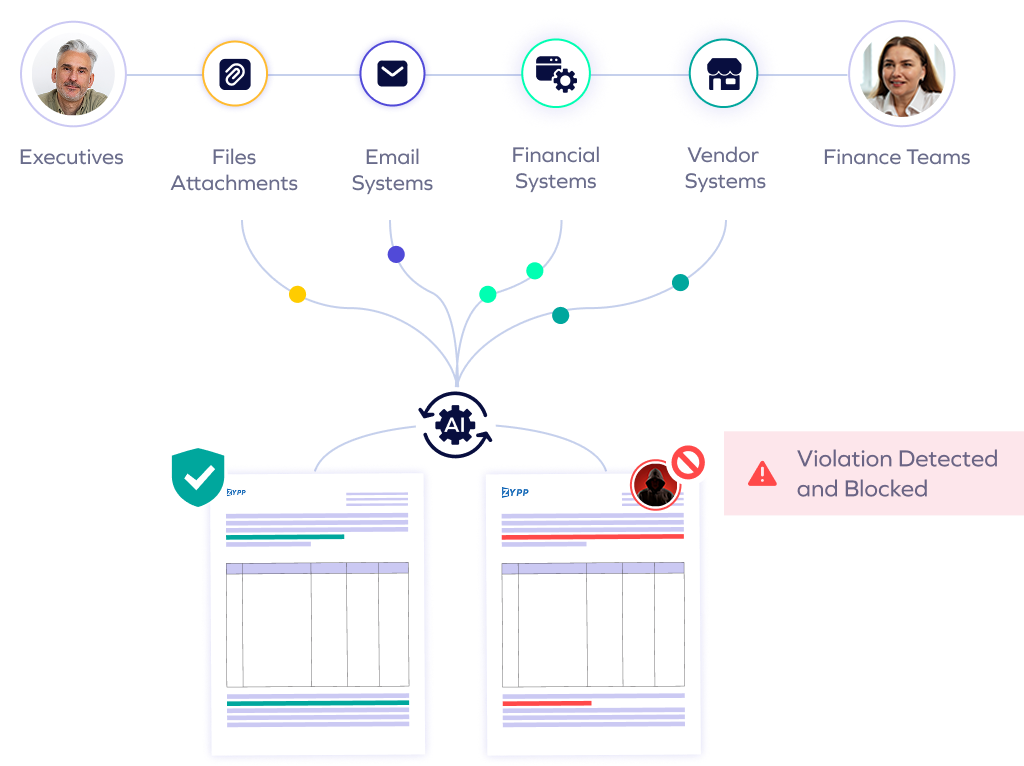
Actively safeguard key accounts such as executives, finance, and vendor-facing roles, where fraud impacts are most severe.
Analyzes hundreds of data points in emails and business systems, including vendor identifying information, profile changes, communications, and invoice data.
Establishes a baseline “digital fingerprint” for each vendor based on historical data and communication patterns and flag deviations.
our approach
Outsmart Vendor Email Compromise with Trustmi
Trustmi delivers a centralized, fully automated solution that safeguards the entire B2B payment lifecycle, proactively addressing the root cause of financial fraud—socially engineered cyberattacks—while reducing manual effort and errors.
Trustmi pulls data from various financial systems and combines it with other critical data points to validate transactions in real time, stopping fraud attempts stemming from social engineering before they cause harm.
Trustmi analyzes patterns across vendors, payment data, emails, and financial documents, detecting sophisticated social engineering tactics and ensuring holistic fraud detection beyond limited channels.
Trustmi seamlessly integrates with your payment ecosystem, ensuring uninterrupted operations while delivering robust protection against socially engineered cyberattacks targeting your payments.
Trusted by Finance and Security Leaders






"Trustmi provided transparency into our payment process to see where cyberattacks and errors were happening and full protection without changing our workflow."
"Like many businesses today, we've experienced cyber attacks on our payment process, but we didn't realize the extent to which we were at risk until we evaluated Trustmi. Now we're confident we'll be able to avoid future attacks with their platform."
"Trustmi's platform is an important tool for our team. Their Payment Flows module increases our payment cycle security, and our team has also managed to cut down the time for preparing payments reports from half a day to half an hour."