Payment approvals are designed to be predictable. Requests are reviewed, documentation is validated, and bank account details are verified before any payment is released.
But after analyzing 260 real-world attacks in the Trustmi Payment Security & Risk Benchmark Report, a consistent gap emerges. And the stakes are only growing. AI-enabled fraud losses are projected to reach $40 billion annually by 2027—up from $12 billion just a few years ago.
The issue isn’t that finance teams are missing something obvious. It’s that the system they’re operating within was never designed for how fraud works today.
- Finance controls are built to catch what looks wrong.
- Modern payment fraud operates by looking right.
That distinction creates the paradox finance teams now face—and it doesn’t exist within finance alone.

Controls are Built for Errors. Fraud is Built for Approval.
Traditional finance controls are designed to identify inconsistencies:
- mismatched vendor details
- incorrect bank information
- missing or incomplete documentation
- deviations from standard process
These are the signals that typically indicate risk. But modern fraud doesn’t introduce inconsistencies. It removes them.
Attackers understand how financial controls work. They know what gets flagged, what gets questioned, and what gets approved. So instead of trying to bypass validation, they design requests to satisfy it.
The goal isn’t to break the process. It’s to move through it cleanly.
The Final Safeguard Is No Longer a Safeguard
Nowhere is this more visible than in bank account validation. Even when everything else appears legitimate, the bank account has traditionally served as the final checkpoint—the last opportunity to detect fraud before money moves. But in modern payment fraud, that assumption no longer holds.
Across real-world incidents, the vast majority of fraudulent payments are sent to accounts that appear entirely legitimate. In more than 90% of cases, the receiving account is:
- active and in good standing
- registered in the vendor’s name
- not flagged as suspicious
In many cases, the account is even located in the same geographic region as the impersonated vendor—removing one of the last remaining signals of risk. Just a year ago, geographical alignment was 60%, and now it’s nearly perfect at 90%. Without mismatched geographical locations of bank accounts and vendor locations, how will finance teams catch fraud?
Today, the final safeguard doesn’t fail—it confirms the fraud.

Documentation Doesn’t Raise Risk. It Removes It.
But by the time finance reaches that final check, the decision has already been shaped. Because the request doesn’t arrive empty—it arrives supported.
Invoices, W-9s, and bank letters are meant to provide assurance. They are the artifacts finance teams rely on to confirm that a request is valid, complete, and ready to process. When those documents are present, and when they match expectations, they reduce friction. They make approval easier.
That is precisely why attackers are using them.
In nearly four out of ten attacks, financial documents are used specifically to make payment requests appear legitimate. And invoices do most of the work. In fact, in the vast majority of those cases, over 90%, fraudulent requests are backed by invoices that fit naturally into existing vendor workflows.
Additional documentation layers build on that foundation:
- W-9s that appear accurate and properly formatted
- bank confirmation letters that validate account changes
- supporting documents that mirror standard onboarding and approval steps
These documents reinforce one another, creating a complete narrative that aligns with how finance expects requests to look. Each piece fits naturally into the workflow, leaving no reason to question the request.
The documents don’t expose the fraud. They justify it.
Everything Checks Out. And That’s the Problem.
Taken together, this is the paradox finance teams are now operating within: the more complete and legitimate a request appears, the more likely it is to be approved. Not because controls are failing, but because they are being satisfied.
Everything checks out. And that’s exactly why the payment goes through.
Approval workflows are no longer just controls—they’re targets. The more complete and legitimate a request appears, the more likely it is to be approved. Not because controls are failing, but because they are being satisfied.
The Bigger Problem: Trust Begins with Email and Identity
It’s not just financial controls that modern fraud are meeting. By the time a request reaches finance, much of the trust has already been established upstream, in systems finance doesn’t own.
Many times, it starts in email. In fact, the majority of these attacks—over 85%—begin there. And they go undetected. Not because security controls are failing, but because there is nothing to detect. There is no malware, no malicious link, no suspicious infrastructure. The message comes from a legitimate account or a convincingly replicated one. It fits within an existing thread. It reflects normal business activity.
From a security perspective, there is no clear signal to flag. So it passes through security controls too.

A Real Life Example
In the Trustmi Benchmark Report, there are two deep dives, and one in particular illustrates how modern fraud is also passing the controls upstream in security: email and identity. In the deep dive, an attacker compromised a vendor’s email account and inserted themselves into an active payment thread. There was no spoofing, no malicious link, no signal for email security to catch. The message came from a legitimate account, within a real conversation.
From a security perspective, nothing was wrong. The account was valid. The activity matched expected behavior. So it went through email security to reach the finance team. And once finance team received the email, it was coming from a trusted source, within an approved channel, aligned with normal business activity.
Trust Is Built Across Email, Identity, Documentation, and Payments
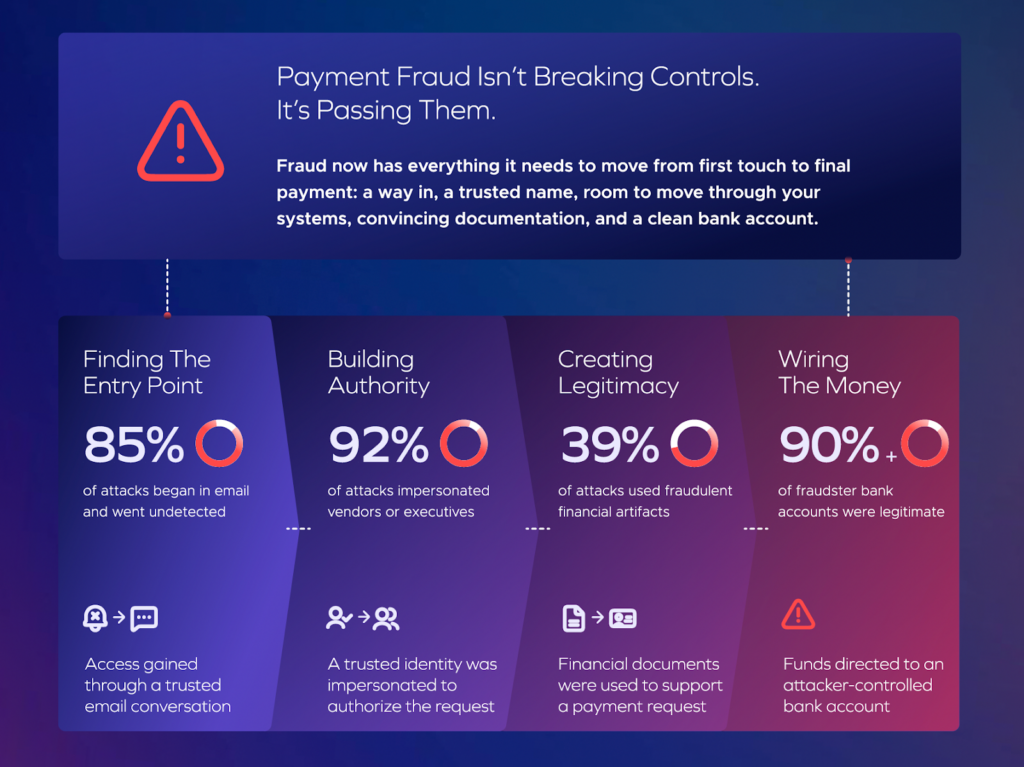
By this point, the pattern is clear:
- 85% begin in email and go undetected
- 92% use a trusted identity to build authority
- 39% are reinforced by financial documentation
- 90%+ end in bank-validated accounts
Modern payment fraud isn’t just passing financial controls. It’s passing security controls as well. In fact, the majority of attacks (59%) use two or more coordinated tactics—spanning systems, workflows, and teams.
The result isn’t a finance failure or a security failure. It’s a shared gap.
Fraud operates across systems, but detection remains siloed. In one out of every three incidents, that disconnect contributes directly to the outcome. Most organizations still lack shared visibility, and only 27% say fraud prevention is jointly owned.
Fraud is coordinated. Defense is not.
As Theresa Payton puts it: “Silos are a fraudster’s best friend.”
Fraud Moves Across Systems. Defense Should Too.
After analyzing hundreds of real-world attacks, the same patterns appear consistently: fraud operates as a coordinated flow across systems, while detection remains fragmented across teams.
That’s why it’s working for attackers.
Because when fraud moves across the entire process, detection has to as well. Finance can no longer rely on validation alone—because validation is no longer a signal of legitimacy.
Detection now requires visibility across the full payment lifecycle: from how requests originate, to how they evolve, to how they are approved. You can’t solve a cross-system fraud problem with siloed controls.
To understand how these attacks actually move across finance and security, download the Trustmi Payment Security & Risk Benchmark Report or join the webinar, Inside the Modern Cyber Fraud Playbook.
And see how leading organizations are aligning teams to detect and stop them, watch the webinar with Theresa Payton.










 Behavioral AI-powered security
Behavioral AI-powered security Protection on day one
Protection on day one 10-15x ROI
10-15x ROI