Every year, the ACH Network moves trillions of dollars in vendor payments, payroll, and business disbursements. And every year, a growing share of those payments is being misdirected by fraud that nobody catches.
To combat this, it’s rolling out its most significant rule changes in years. But Nacha’s 2026 rules changes are about more than compliance. They reflect a larger reality: payment fraud has become harder to detect, easier to scale, and more costly than many organizations realize.
This article explains what is changing, who it affects, and what it requires. More importantly, it reveals the financial risk your organization may already be carrying.

What Is Changing, When, and Who Does It Affect?
Nacha’s fraud monitoring requirements are expanding significantly, shifting from a narrow, use-case-specific expectation to a broader, network-wide obligation.
What is changing?
Previously, businesses were only expected to maintain a “commercially reasonable” fraud detection system for internet-initiated consumer debits (WEB entries) and Micro-Entries. Now, Nacha requires non-consumer organizations involved in ACH origination to implement a documented, risk-based fraud monitoring program that covers the full payment lifecycle.
In plain terms: fraud monitoring is no longer limited to a narrow set of ACH transactions. It is becoming a broader expectation for how business payments are reviewed and protected before money moves.
When are the changes taking effect?
Phase 1 took effect on March 20,2026.
Phase 2 takes effect on June 22, 2026, and eliminates the volume threshold completely.
Who does it affect?
The new Nacha rule changes apply to non-consumer ACH participants, including business Originators, ODFIs, Third-Party Service Providers (TPSPs), and Third-Party Senders (TPSs).
In practical terms: if your organization helps create, process, submit, or manage business ACH payments, these requirements likely apply to you.
What does this mean for your business?
ACH is one of the most common ways businesses move money in the U.S.—from vendor payments and payroll to recurring transfers. That means Nacha’s expanded fraud monitoring rules affect far more organizations than many realize, requiring stronger controls to detect deceptive payments, monitor risk, and document compliance.
The Risks Behind the Rule Changes
As fraud monitoring requirements expand, failing to adapt can introduce organizations to regulatory and operational risks.
Regulatory Risk
Nacha enforces its rules through a structured escalation system. Initial violations are typically resolved without penalty if the business corrects them quickly. However, unresolved or repeated violations move through three classes of consequences.
- Class 1 – fines of up to $1,000
- Class 2 – fines of up to $2,500
- Class 3 – fines up to $5,000
In some extreme cases, persistently unresolved Class 3 violations can reach up to $500,000 per month. In this case, Nacha is authorized to report those violations to ACH Operators and federal and state regulators.
For organizations, this goes beyond financial penalties. Regulatory escalation can trigger external scrutiny, damage banking relationships, or introduce long-term compliance oversight that limits operational flexibility.
Operational Risk
Some of those fines may seem small to large enterprises, but if your ODFI determines that your fraud controls are inadequate, it can restrict or suspend your ACH origination access. For any business that runs payroll, vendor payments, or treasury operations over ACH, that is an existential operational problem.
In practice, this means that payroll stops, vendor invoices go unpaid, and treasury operations freeze. Non-Consumer Originators can have their ACH network access revoked, be subject to the violation process, and potentially incur fines or penalty fees.
Over the past decade, we’ve seen this change reflect a broader pattern in cybersecurity. What was once loosely enforced and rarely discussed is now becoming standardized, monitored, and increasingly visible. Just as breach disclosure laws forced organizations to take data security seriously, Nacha’s expanded requirements signal a move toward greater accountability and transparency in payment fraud prevention.
A Brief Overview of What Nacha Requires
With that level of risk on the table, understanding how to comply becomes critical. NACAHA now requires behavioral, cross-system fraud detection across the full payment lifecycle. This is a different category from callbacks, bank account validation, or approval workflows.
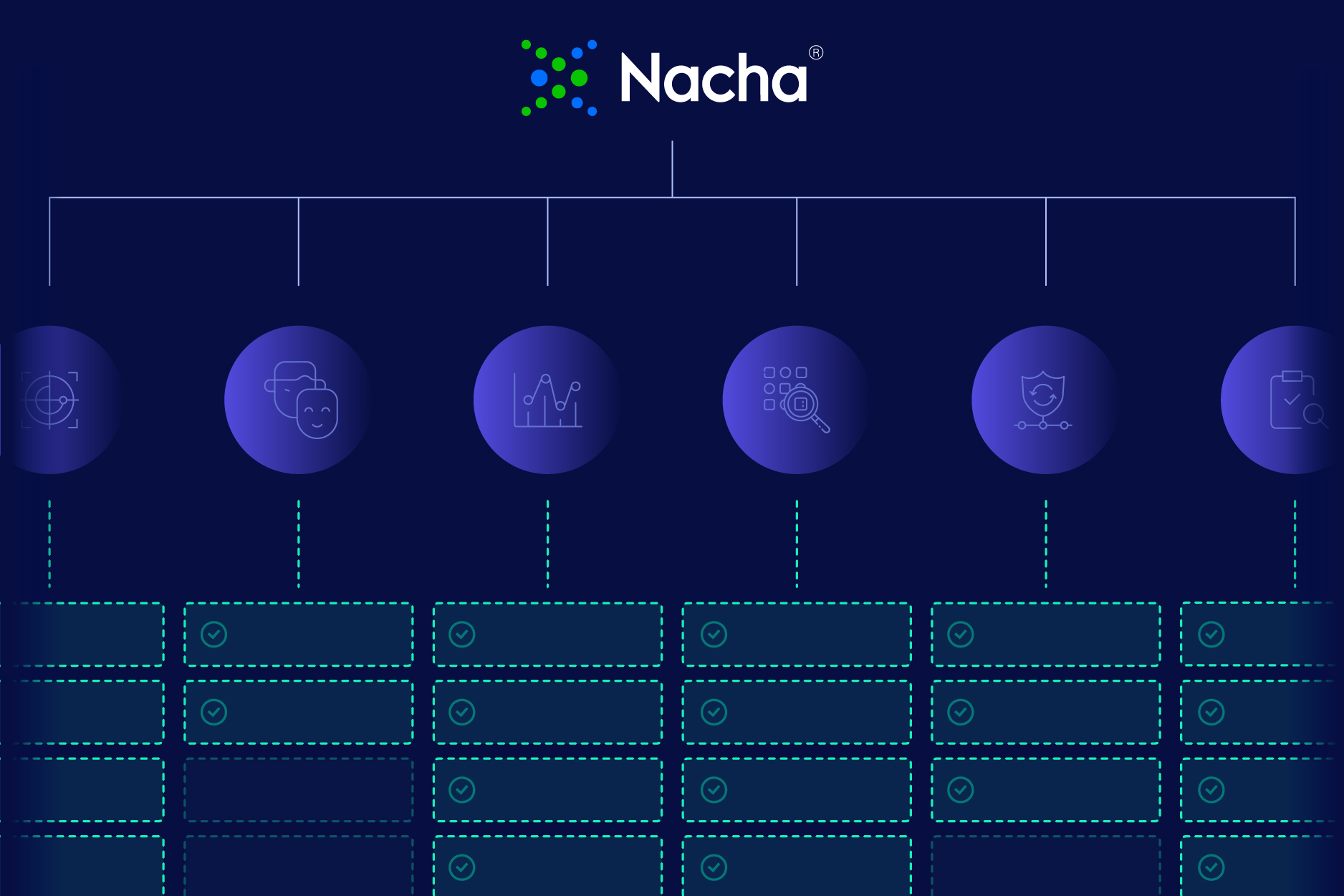
The practical implication is highlighted in the table below:

Finance teams that modernize these areas will be better positioned to reduce fraud risk, improve payment confidence, and meet expanding NACHA expectations.
What Nacha Requires: A Comprehensive Look
In this section we go deeper into each Nacha requirement, what it demands in practice, and why this update is a structural change rather than an incremental one.
Risk-Based Fraud Monitoring and Prioritization
Nacha’s updated rules require organizations across the ACH ecosystem—including Originators, ODFIs, TPSPs, TPSs, and RDFIs—to implement risk-based fraud monitoring processes designed to identify fraudulent entries.
In practice, that means payments cannot all be treated the same. A recurring vendor paid on a normal schedule carries a different risk profile than a first-time payee receiving a large payment immediately after a banking detail change.
The next step is prioritization. Organizations must determine which transactions and activities present the highest risk and focus monitoring accordingly.
This is a meaningful shift in how finance teams approach fraud. The question is no longer only: did this payment pass every control? It is how much risk does this transaction carry, and does it require intervention?
Detecting False Pretenses
If you’ve never heard of False Pretenses—or at least not used in this context—you’re not alone. False Pretenses is a new term by Nacha that defines anything that induces a payment through misrepresentation of identity, authority, or account ownership.
Three fraud types fall squarely here. A fraudster impersonating a vendor to submit new banking details, a spoofed or compromised email redirecting a payment, and an attacker posing as an employee to change payroll information.
This pattern is more common than many teams realize. The Trustmi 2026 Benchmark Report shows that 92% of attacks begin with a trusted identity. In 90% of cases the bank account is valid and in good standing. As a result, these payments pass standard validation checks because nothing about the data itself is incorrect.
Establishing Baselines for Transaction Activity
Nacha’s own guidance states that regular fraud detection monitoring can establish baselines of typical activity to make atypical activity easier to identify.
A baseline is what gives anomaly detection meaning. Without knowing how a specific vendor communicates, what their invoices typically look like, or how often their banking details change, any deviation becomes hard to distinguish from normal variation. With behavioral baselines in place, a sudden change in communication pattern or an out-of-cycle banking update becomes a signal.
Detecting Anomalies
Once behavioral baselines exist, the next task is identifying when transactions deviate from them. Nacha highlights specific signals, including:
- unusual dollar amounts
- abnormal volumes
- account number changes
- timing anomalies
- mismatches between transaction type and account characteristics
The risk usually emerges when these signals are connected. A payment might involve a recently updated bank account, arrive outside normal timing, and be tied to a vendor whose communication context has changed. Together, they indicate abnormal behavior.
Since many of these transactions do not break predefined rules, detection depends on cross-system correlation to identify patterns that fall outside normal behavior.
Continuous Monitoring
Another critical requirement is continuous monitoring. A vendor impersonation attack may begin weeks before a payment instruction is ever submitted and a BEC scheme may build over months. By the time a fraudulent request reaches your finance team, everything downstream may look completely clean because the fraud happened earlier, in the communication layer that standard controls do not watch.
Monitoring must operate before and during payment processing. The full lifecycle needs coverage: from vendor onboarding through banking detail changes and final payment execution.
Documentation and Annual Review
Nacha requires organizations to document their fraud monitoring processes, maintain written records, and review them at least annually to keep pace with evolving threats.
For many teams, the challenge is operational. When controls sit across multiple systems, documentation can become fragmented and audits more time-consuming. Without a centralized view of how payments are monitored end-to-end, maintaining a repeatable review process becomes significantly harder.
Screening Outbound ACH Originations
ODFIs and Business Originators must screen outbound ACH originations for fraud signals prior to submission.
In practice, this means organizations need a reliable way to pause, review, or challenge suspicious payments before funds are released. Many payment workflows still process transactions straight through, leaving limited opportunity to intervene once risk is identified.
That is why pre-payment validation matters: effective fraud detection must happen before money moves, not after funds have settled.

Why This Is Bigger Than Compliance
These requirements are not appearing in a vacuum. They reflect how modern payment fraud now bypasses controls that once felt sufficient. And today’s fraud doesn’t break the process—it blends into it. As The Trustmi 2026 Payment Security Risk Benchmark Report shows, most attacks begin with trusted identities and are supported by legitimate-looking documentation. What’s missing isn’t another control, but context.
That’s why Nacha is pushing for stronger monitoring: not just verifying payments, but recognizing when something doesn’t add up. Finance teams that treat the 2026 deadline as a compliance checkbox may pass the audit. But they risk missing the fraud already moving through their workflows.
The real opportunity is bigger: reducing hidden payment risk before it turns into loss.
If you’re preparing for the new NACHA requirements, see how Trustmi helps finance teams strengthen fraud monitoring, reduce risk, and stay audit-ready.









 Behavioral AI-powered security
Behavioral AI-powered security Protection on day one
Protection on day one 10-15x ROI
10-15x ROI