Quick Summary
This guide reviews seven leading business email compromise (BEC) tools and explains how each protects against email-based attacks. We also explore how many organizations extend BEC protection into payment workflows using behavioral AI designed to reduce fraud risk beyond the inbox.
Are Your Current Business Email Compromise Tools Protecting Your Payments?
With BEC now driving over 37 percent of all cybercrime losses and causing nearly $2.1 billion in damages, the question isn’t whether you need protection. It’s determining which tools can actually detect today’s AI-driven impersonation and payment-diversion attacks.
Most teams begin with email security, but many attacks continue beyond the inbox into vendor records, approvals, invoices, and payment systems, taking advantage of gaps between disconnected workflows. While BEC can create many consequences across the enterprise, payment fraud remains one of the most financially damaging and often requires controls beyond traditional email security tools.
According to Trustmi’s latest benchmark report, 85% of B2B payment fraud begins in email and is not stopped at the email layer alone. That means many organizations secure the inbox while remaining exposed where money actually moves.
In this Trustmi guide, we review seven leading BEC tools and explain how each supports email protection and identity security. We also explore why many organizations extend those defenses into payment workflows.
Why Listen to Us?
Trustmi secures the entire payment lifecycle for enterprises, protecting more than $240B in business payments. Our cross-industry experience gives us deep insights into how fraud actually occurs and which tools truly stop it, allowing us to clearly explain each solution’s strengths, limitations, and role in a complete defense strategy.

What Is a Business Email Compromise Tool?
Business Email Compromise is a type of attack where criminals impersonate trusted people, such as executives, vendors, or employees, to manipulate others into taking actions they normally would not.
Those actions can vary. They may involve sharing credentials, downloading malware, exposing sensitive data, changing payment details, or sending money. Because BEC attacks begin through email, most BEC tools focus on protecting that layer. They are designed to detect and block the most common threats that arrive through the inbox:
- phishing emails
- malicious links
- malware attachments
- spoofed domains
- suspicious senders
- compromised accounts
These capabilities are essential, and they’re highly effective at reducing risk at the email and identity layers. But as threats evolve, especially with the sophistication of AI, many organizations need to extend that protection into approval processes and payment workflows.
Why Extend BEC Protection Into Payment Workflows
Most BEC tools are designed to operate within the email and identity layers. They block malicious messages, detect compromised accounts, and stop impersonation attempts at the inbox level. However, these tools are primarily designed for the email and identity layers and may not address every form of financially motivated attack, particularly those that unfold beyond the inbox. In fact, a Trustmi report reviewing 260 real-world attacks, found that 85% of payment fraud attacks start in email and go undetected.
Attackers know email filters are catching their initial attempts, so they shift tactics. They compromise vendor accounts, manipulate ERP records, alter invoices after approval, or build trust through weeks of legitimate-seeming communication before introducing fraudulent payment requests.
According to the Trustmi 2025 Socially Engineered Fraud & Risk Report, 70% of payment fraud incidents spanned multiple systems (e.g., email + ERP + procurement). These multi-system attacks often involve compromised vendor accounts, subtle banking detail changes, or executive impersonation. Some attacks appear legitimate enough to evade controls focused on email content or sender reputation.
BEC tools are highly effective at protecting the email and identity layers. Many organizations add controls for payment workflows, where fraud can emerge after a request appears legitimate.
- No Financial Context: Can’t correlate email requests with ERP data, vendor payment history, or banking information
- Limited Visibility: Protection stops at the inbox and identity layer, leaving procurement, approval, and payment stages vulnerable
- Manual Verification Required: Organizations still rely on stressful, unreliable manual callbacks and checks
- Fragmented Tools: Lack integration with financial systems, vendor relationships, and payment workflows
To truly stop payment fraud, organizations need solutions that monitor the entire payment lifecycle, from vendor onboarding through payment execution, integrating with ERPs, procurement systems, and financial platforms to detect behavioral anomalies and verify every payment before money moves.
Trustmi: The Payment Fraud Prevention Layer That Complements BEC Tools
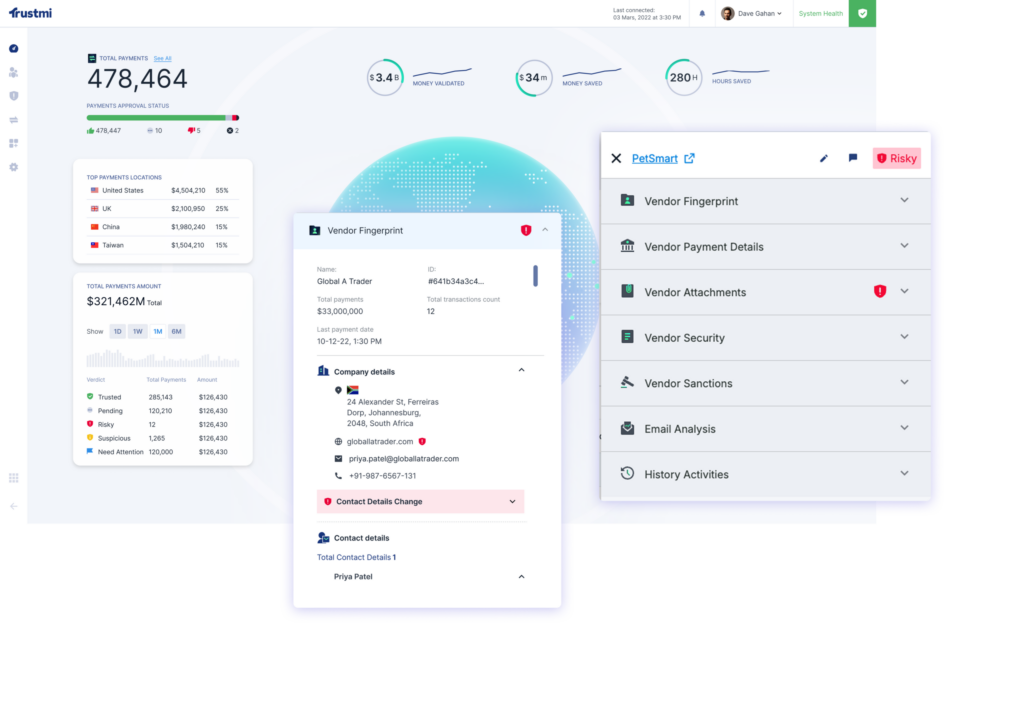
While BEC tools protect your inbox and identity systems, Trustmi is the first end-to-end B2B payment security platform, purpose-built to prevent the socially engineered fraud that traditional BEC tools can miss.
Using Behavioral AI, Trustmi monitors and validates every step of the payment process to detect and stop fraudulent transactions across vendor systems, ERPs, procurement platforms, and payment workflows.
Here’s how Trustmi complements your BEC tools:
- End-to-End Visibility: Monitors the entire payment lifecycle across vendors, communications, financial systems, procurement, ERP, and payments
- Behavioral AI Detection: Purpose-built to catch socially engineered attacks targeting B2B payments—BEC, vendor impersonation, account takeover, and fraudulent bank detail changes
- Financial Context Integration: Correlates email data with ERP, vendor, and payment history to detect sophisticated fraud schemes
- Automated Payment Validation: Verifies every payment against established patterns before money moves, eliminating manual callbacks
- Seamless Integration: API-based connection that works with your existing tools without disrupting workflow
7 Top BEC Tools to Protect Email and Identity
Each tool protects a different layer of email and identity security. The table below highlights their core strengths at a glance.
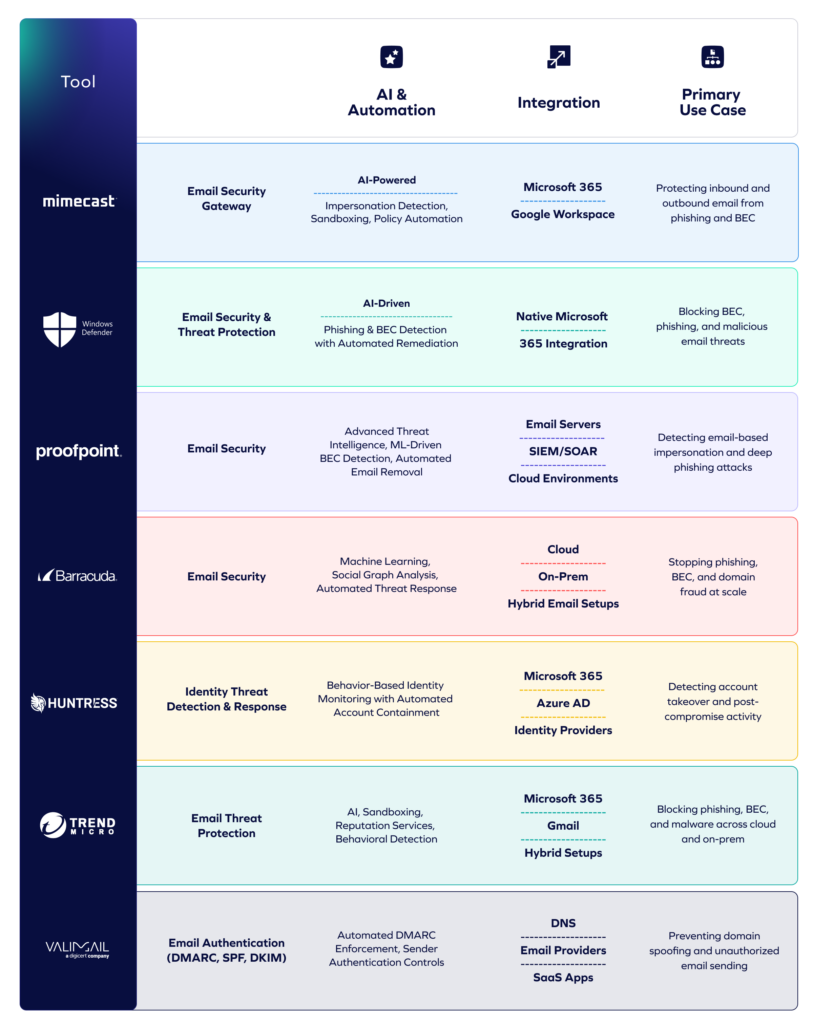
Now, let’s look at each tool in detail.
1. Mimecast Email Security
Many organizations pair platforms like Mimecast with payment-layer protection for broader defense.
Best for: Large organizations needing strong, enterprise-grade protection against phishing, impersonation, and BEC within their email environment.
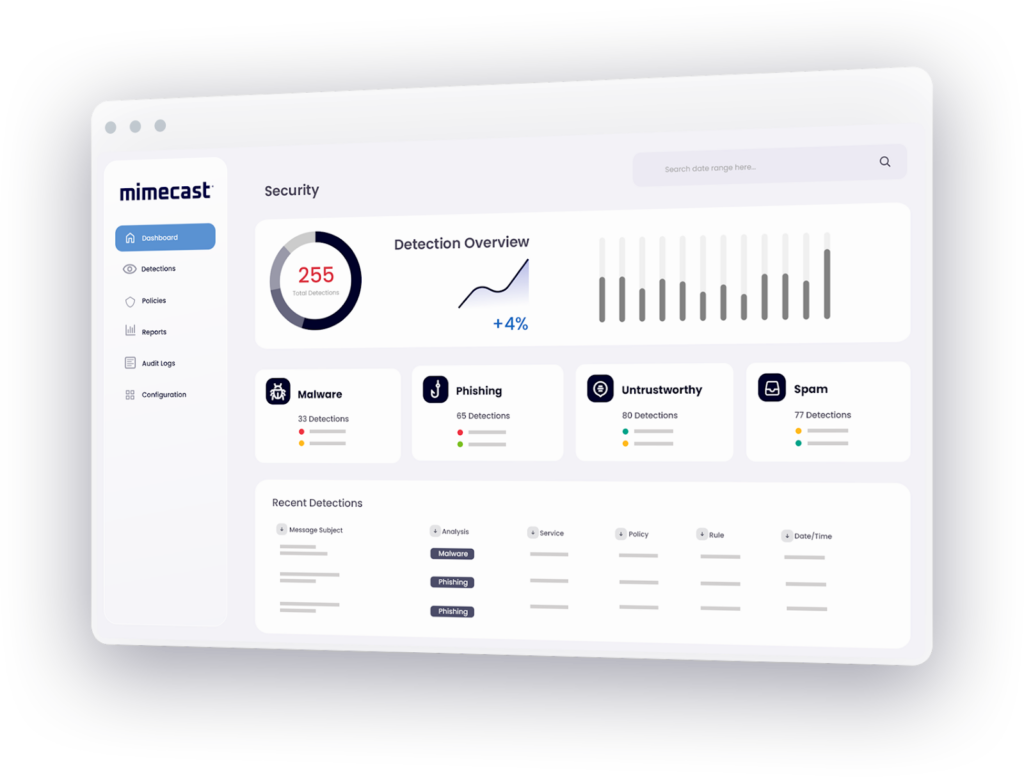
Mimecast protects email systems against phishing, spoofing, BEC and malware using multiple detection engines and AI-driven threat intelligence.
Because its core strength is the email channel, it remains one of the strongest in message protection and policy management, though it doesn’t directly monitor vendor systems or payment-approval workflows.
Key Features
- Advanced URL & attachment scanning: Inspects every link and file in email traffic to catch hidden malware or phishing traps.
- Impersonation and domain spoof detection: Flags lookalike domains or forged senders that attempt to mirror trusted vendors or executives.
- Outbound email protection: Monitors outgoing messages to prevent compromised accounts from being used for fraudulent solicitations or payment-diversion attempts.
- Cloud-based deployment with Microsoft 365/Google Workspace support: Integrates smoothly with major platforms for fast onboarding and email continuity.
- Centralized policy and reporting dashboard: Gives security teams one place to set detailed rules, monitor risk levels, and control how email traffic is managed across the organization.
Pricing
Mimecast Email Security pricing is customized based on your business needs.
Pros
- Effective at blocking phishing and fraud-oriented email threats
- Strong URL and attachment security using sandboxing
- Easily integrates with Microsoft 365 and Google Workspace
- Rich policy controls and reporting for enterprise use
Cons
- Can be expensive for smaller teams
- Policy tuning may require specialized security expertise
How Mimecast works with Trustmi
Mimecast provides strong protection at the email layer, helping organizations stop phishing, impersonation, and BEC attacks before they reach the inbox. In fact, Mimecast has partnered with Trustmi to extend that protection into financial workflows, addressing the risk of fraudulent and misdirected payments that can occur after an attack appears legitimate.
“AI-driven attacks are making fraud more convincing and harder to detect at the entry point,” said Jules Martin, VP Technology Alliances, Mimecast.

“AI-driven attacks are making fraud more convincing and harder to detect at the entry point,” said Jules Martin, VP Technology Alliances, Mimecast. “The Mimecast and Trustmi integration extends email and BEC protection into financial workflows where real damage can occur – preventing costly, fraudulent, and misdirected payments resulting from socially engineered attacks. This integration helps give security and finance teams a more complete defense against modern threats.”
2. Microsoft Defender for Office 365
Best for: Organizations that already use Microsoft 365 and want native, AI-powered email protection for preventing BEC, impersonation, and malicious link/attachment attacks.
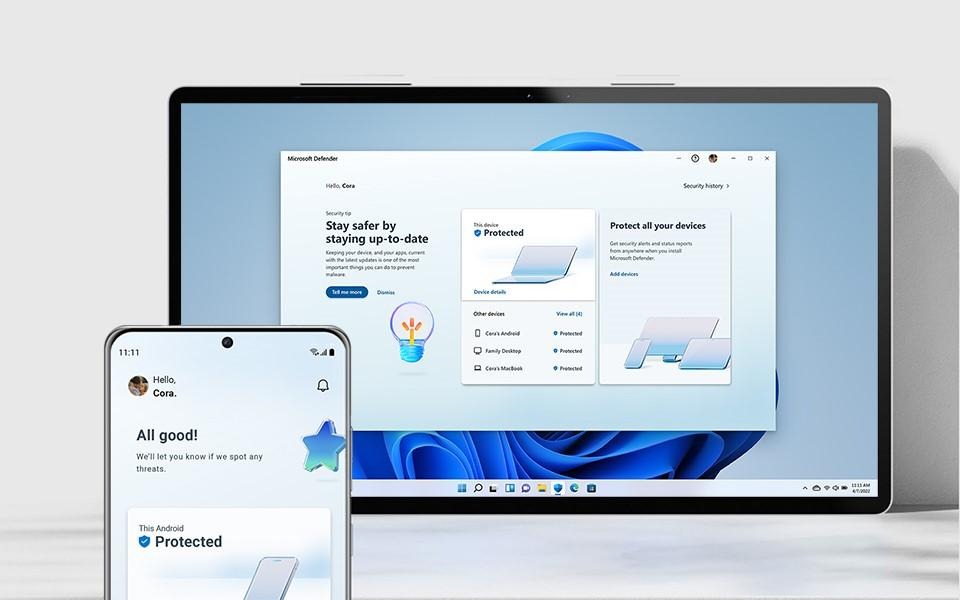
Microsoft Defender for Office 365 is a comprehensive security solution built into the Microsoft 365 ecosystem. It leverages AI, threat intelligence, and machine learning to detect phishing, account compromise, and BEC attempts.
The tool not only prevents malicious emails from hitting inboxes but also allows security teams to investigate, quarantine, and remediate threats efficiently.
Key Features
- AI-Powered Anti-Phishing: Uses generative AI and “mailbox intelligence” to detect user and domain impersonation.
- Spoof Intelligence: Analyzes sender domains and email authentication signals (SPF/DKIM/DMARC) to prevent spoofed BEC attacks.
- Safe Links / Time-of-Click Protection: Scans links in email in real time, even after delivery, to block malicious redirections.
- Anti-Malware Scanning: Scans attachments with multi-layered malware detection, heuristic analysis, and cloud-based threat intelligence.
- Compromised Account Response: Detects compromised mailboxes, isolates devices, and supports post-incident remediation.
Pricing
Microsoft Defender for Office 365 offers two plans with annual commitments:
- Plan 1 ($2.00 per user/month): Includes protection for email, Teams, SharePoint, OneDrive, real-time protection for malicious links/QR codes, zero-day malware protection, and real-time reporting.
- Plan 2 ($5.00 per user/month): Includes all Plan 1 features plus advanced cyberthreat hunting, attack simulation training, automated response, and cross-domain XDR capabilities.
Also included in Microsoft 365 E5 Security.
Pros
- Seamless integration with Microsoft 365 suite
- Established phishing, malware and BEC protection
- Single vendor support and licensing simplicity
- Native support for Teams, SharePoint and OneDrive
Cons
- False positives occasionally require manual review
- Advanced settings may overwhelm non-technical users
- System resource demands sometimes cause noticeable system slowdowns
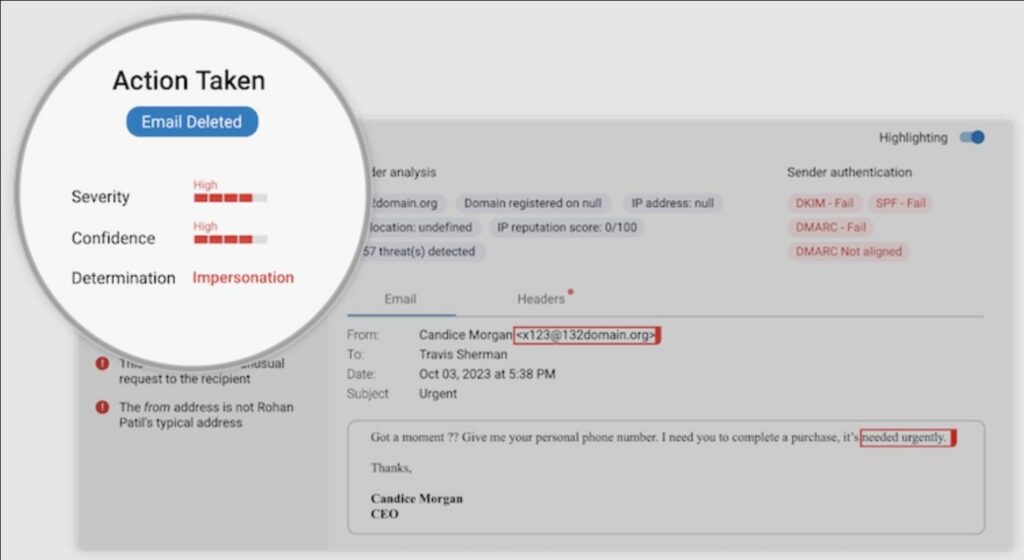
3. Proofpoint Email Protection
Best for: Enterprises needing advanced email threat detection and strong BEC protection with deep visibility into impersonation attempts.
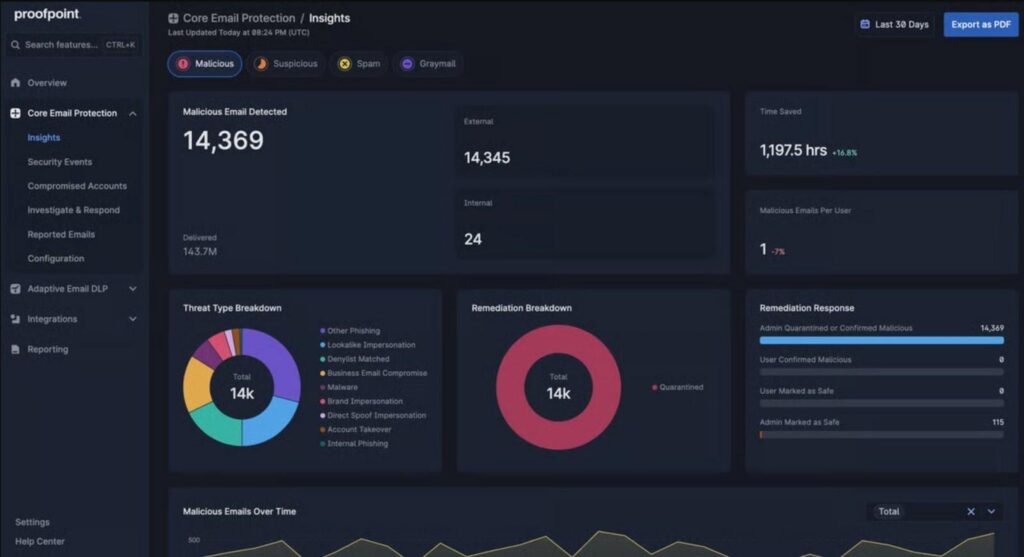
Proofpoint Email Protection is a leading email security platform that defends against phishing, malware, and business email compromise using advanced threat intelligence and machine learning.
It analyzes sender identity, domain behavior, message intent, and communication context to detect sophisticated impersonation attempts that bypass basic filters.
Key Features
- Advanced Threat Intelligence: Continuously updates defenses using data from trillions of processed emails.
- Predictive URL Defense: Sandboxes suspicious links in real time before users click, preventing post-delivery attacks.
- Attachment Sandboxing: Analyzes attachments in isolated environments to detect malware or malicious payloads.
- BEC & Impersonation Protection: Uses behavioral AI, header analysis, and DMARC feedback loops to catch forged or spoofed emails.
- Automated Email Remediation: Automatically quarantines or pulls dangerous emails post-delivery to stop phishing campaigns.
Pricing
Proofpoint offers customized enterprise pricing based on the number of users and required features.
Pros
- Excellent BEC detection with strong identity analysis
- Strong sandboxing that catches advanced payload threats
- Rich policy customization for complex security needs
- Enterprise-proven with large-scale threat intelligence
Cons
- Primarily focused on email security rather than end-to-end payment workflow controls
- Can be costly with multiple advanced add-on modules
4. Barracuda Email Protection
Best for: Organizations needing scalable, AI-powered email security that covers phishing, impersonation, domain fraud and BEC.
Barracuda Email Protection is a full-spectrum email defense solution designed to block modern threats like business email compromise, vendor impersonation and credential abuse. Since email remains the primary entry point for payment diversion and vendor account fraud, Barracuda helps teams fill the visibility and response gaps left by built-in mail filters.
Key Features
- AI-Powered Threat Detection: Uses machine learning and social graphing to detect abnormal sender behavior and social engineering.
- Advanced BEC Protection: Leverages behavioral AI, urgency detection, and impersonation analysis to block BEC attacks.
- Sandboxing & URL Protection: Scans attachments and links in real time, detecting decoys and malicious redirects.
- Flexible Deployment Options: Supports cloud, hybrid, or on-prem deployments with granular controls tailored to your environment.
- Integrated Threat Intelligence: Shares insights with SIEM, XDR, and collaboration tools to stop attacks across your security ecosystem.
Pricing
Barracuda offers three pricing plans tailored to the number of users: one for businesses with less than 50 users, another for those with 50 or more users, and a third plan for Managed Service Providers (MSPs) and resellers. For exact pricing, contact Barracuda.
Pros
- Strong multi-layer BEC and impersonation defense
- Comprehensive domain-fraud and typosquat detection
- Automated remediation lowers security team workload
- Flexible deployment options and cloud scalability
Cons
- Interface can feel dated compared with newer platforms
- Complex rule creation with hard-to-understand priority order
- Self-release of quarantined emails is sometimes unavailable
5. Huntress Managed ITDR
Best for: Organizations needing strong protection against BEC, account takeover and identity-based intrusions in Microsoft 365.
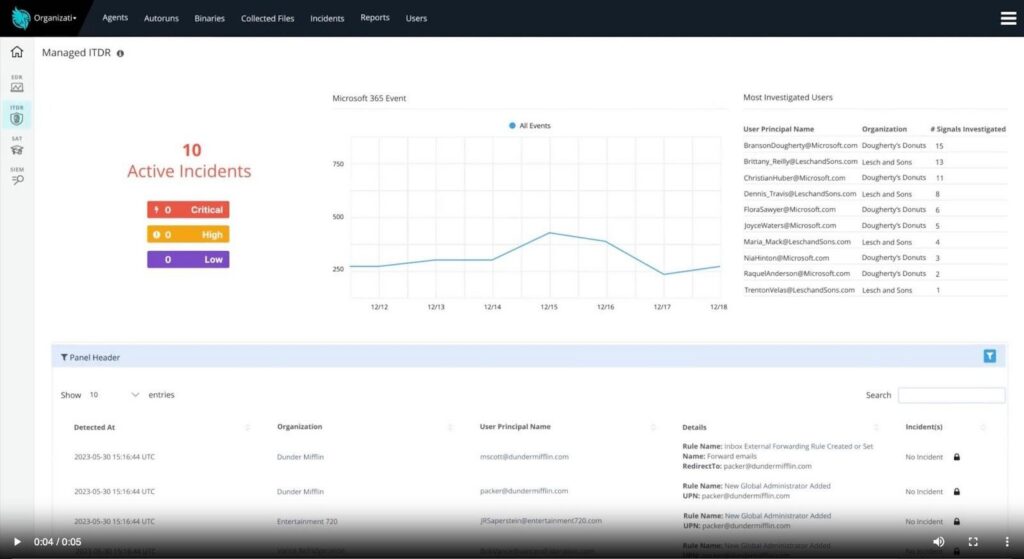
Huntress Managed ITDR is a fully managed identity threat detection and response solution focused on identity-based threats and post-compromise activity in Microsoft 365 environments.
Rather than operating as a traditional email gateway, it helps stop attacks after a user account is compromised by detecting behaviors such as session hijacking, rogue OAuth apps, and hidden inbox rule changes.
Key Features
- Session Hijack Detection: Spots suspicious session tokens, unusual locations or proxy usage that indicate an attacker logging in.
- Rogue OAuth App Monitoring: Flags malicious or over-privileged apps that attackers use to maintain access even after password resets.
- Inbox and Workflow Rule Analysis: Detects forwarding rules, hidden filters and mailbox changes used to divert communication.
- 24/7 Analyst-Backed SOC: Human experts verify threats to reduce noise and provide clear, actionable alerts.
- Automated Containment: Quickly isolates compromised accounts and removes malicious permissions to limit attacker movement.
Pricing
Custom pricing based on identities and environment size.
Pros
- Strong identity-focused approach beyond email filtering
- Effective detection of post-compromise activity
- Low false-positive rate (< 5%)
- Deep identity protection beyond just email security
Cons
- Mainly focused on Microsoft 365 environments
- Does not address vendor verification or payment-flow fraud on its own
6. Trend Micro Email Security
Best for: Organizations seeking layered email threat protection across phishing, vendor impersonation, and BEC in mixed cloud and on-prem environments.
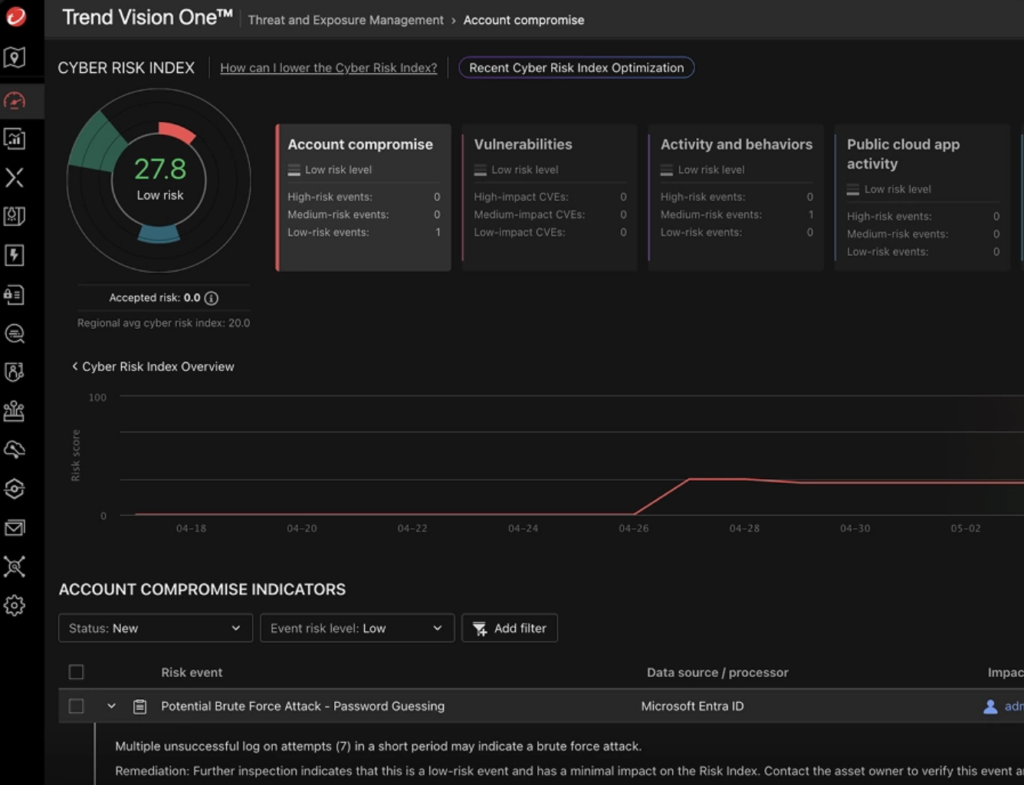
Trend Micro Email Security combines machine learning, sandbox analysis and reputation intelligence to defend against phishing, BEC scams, spoofing and social-engineering attacks.
While strong for email channel defense, it does not natively cover vendor system verification or cross-system payment workflows.
Key Features
- Integrated phishing and BEC detection: Learns high-profile users and examines message metadata to catch impersonation.
- Multi-engine threat scanning: Combines AI, sandboxing and reputation services to identify unknown malware and malicious URLs.
- Outbound email and DLP controls: Monitors outgoing traffic to prevent data leakage or internal account misuse.
- Domain spoofing and typosquat protection: Flags lookalike domains and ensures display names aren’t mimicked by attackers.
- Cloud and on-premise deployment support: Works with Microsoft 365, Gmail and mixed infrastructures for broad email protection.
Pricing
Custom quote based on user count and modules.
Pros
- Strong phishing and BEC detection across inboxes
- Advanced URL/attachment sandboxing for unknown threats
- Outbound controls reduce internal misuse risk
- Flexible deployment for cloud or on-prem environments
Cons
- Lacks vendor/payment workflow coverage
- Requires additional tools for vendor identity and bank detail verification
7. Valimail
Best for: Organizations that want to enforce sender authentication (SPF, DKIM, DMARC) to stop domain spoofing and impersonation risk from BEC attacks.
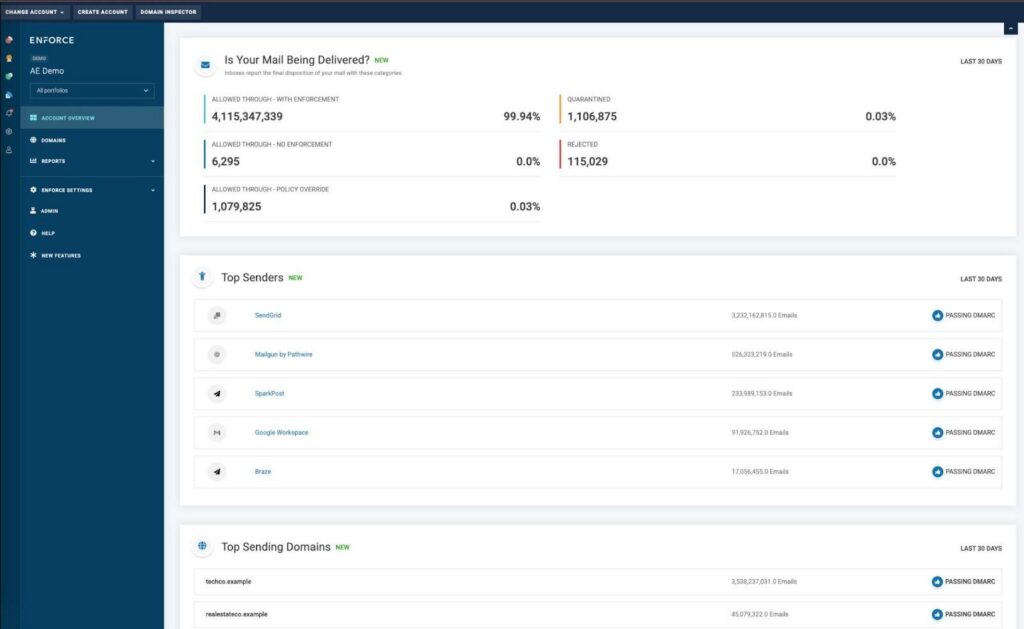
Valimail is an email authentication platform that automates DMARC, SPF, and DKIM management to protect your domain from spoofing and phishing.
It offers real-time visibility into who’s sending email on your behalf, allows you to enforce strict authentication policies, and ensures that only trusted senders can use your domain.
Key Features
- Automated DMARC Enforcement: Guides SPF/DKIM setup, prevents spoofed email domains, and accelerates compliance.
- Real-Time Domain Fraud Monitoring: Tracks and quarantines unauthorized senders or third-party services using your domain name.
- Inbound & Outbound Authentication: Ensures both your outgoing mail and inbound messages from others are properly authenticated.
- Shadow IT Visibility: Exposes hidden email sending services or rogue apps that may impersonate your brand.
- Detailed Reporting & Dashboard: Aggregates DMARC reports into actionable insights for security teams.
Pricing
Requires a custom quote based on domains, sending volume, and enforcement level.
Pros
- Automates complex authentication setup efficiently
- Protects your domain from spoofing and impersonation
- Improves deliverability when authentication is strong
- Scalable across large organizations and multiple domains
Cons
- Requires DNS and email infrastructure changes for full effect
- May need supplementary tools for end-to-end fraud protection
Strengthen Your BEC Defense With Trustmi
Business Email Compromise tools are critical in preventing fraud at the email and identity layers. But stopping BEC requires more than just email filters. While traditional tools protect inboxes, attackers often exploit vendor systems and payment workflows.
Trustmi fills this gap with behavioral AI that verifies vendor identity, detects cross-system anomalies, and intercepts suspicious transactions, ensuring your organization remains protected from financial loss, even after a BEC attack slips through.Ready to close the gap between email security and payment security?Request a Trustmi demo and see how we stop the fraud attempts that slip past even the strongest BEC tools.










 Behavioral AI-powered security
Behavioral AI-powered security Protection on day one
Protection on day one 10-15x ROI
10-15x ROI