Invoice fraud isn’t new—but the way it succeeds has changed.
The rise of generative AI has made invoice fraud easier to execute at scale. Attackers can now produce highly convincing invoices, supporting documents, and vendor communications that align with real workflows, making fraudulent requests harder to distinguish.
At the same time, vendor ecosystems are expanding and payment cycles are accelerating. Accounts payable teams are processing more transactions, across more systems, under greater time pressure—creating the ideal conditions for well-crafted fraud to blend in.
In fact, 39% of B2B payment fraud attacks include fraudulent financial artifacts such as invoices, W-9s, or bank documents, reinforcing payment requests within normal accounts payable workflows.
The result is a subtle but critical shift:
In many cases, fraud doesn’t bypass controls—it passes them.
This article breaks down how modern invoice fraud operates inside accounts payable workflows, why it continues to succeed despite existing safeguards, and what finance teams can do to reduce exposure.
What Is Invoice Fraud?
At a basic level, invoice fraud involves submitting a request for payment that isn’t legitimate. Whether that’s through a fake invoice, altered details, or manipulated payment instructions.
Instead, it shows up embedded within real vendor relationships and familiar workflows. A payment request may reference a known supplier, match expected timing, and include documentation that appears complete, which makes it difficult to distinguish from routine activity.
In more and more cases, the invoice itself is only one part of the attack. Threat actors often pair it with compromised vendor communications, updated banking details, or supporting documents designed to reinforce legitimacy.
This is where the risk is evolving.. According to Trustmi’s Payment Security & Risk Benchmark Report, in 92% of cases, the primary financial artifact is a fake invoice. But the growing trend is that these invoices are accompanied by additional materials such as W-9s or bank confirmations. The elements work together to create requests that feel routine, verified, and ready for approval.
As a result, invoice fraud is no longer just about identifying incorrect invoices. It’s about identifying requests that appear valid—across multiple layers of documentation and communication.
Why Invoice Fraud is Increasing
The rise in invoice fraud isn’t just a function of more transactions. It’s a result of how payment operations have evolved.
As organizations scale vendor ecosystems and accelerate payment cycles, accounts payable workflows have become faster, more distributed, and more dependent on digital inputs. This creates more opportunities for fraudulent requests to enter—and fewer opportunities to scrutinize them manually.
At the same time, generative AI is changing how these attacks are executed. Attackers can now produce highly consistent invoices, supporting documents, and vendor communications that align with real business activity—making fraudulent requests far more difficult to distinguish from legitimate ones.
But the most important shift is structural.
Most payment controls were designed for a world where fraud was easier to spot—where anomalies stood out, and verification steps could reliably catch inconsistencies. Today, attackers are designing requests to fit those expectations, not break them.
As a result, invoice fraud is no longer driven by obvious deception. It succeeds by aligning with how accounts payable processes are built to operate.
6 Common Types of Invoice Fraud to Watch For
These categories reflect how invoice fraud typically appears within accounts payable workflows.
In practice, they rarely occur in isolation. Many attacks combine multiple elements—emails, invoices, and supporting documentation—into a single request designed to move through approval processes without friction.
1. Fake Invoices
Fake invoices involve billing a company for goods or services that were never delivered. These submissions may originate from unknown vendors or impersonators attempting to exploit gaps in vendor onboarding or invoice validation processes.
2. Duplicate Invoices
Duplicate invoice fraud occurs when the same invoice is submitted multiple times for payment. In high-volume AP environments, duplicate submissions can slip through when invoice validation practices vary across systems, entities, or payment cycles.
3. Overbilling or Inflated Charges
Some schemes involve invoices with inflated quantities, pricing, or service charges. Without consistent contract validation or pricing oversight, these discrepancies can accumulate gradually across vendor relationships.
4. Vendor Impersonation and Phishing
Fraudsters frequently impersonate vendors or compromise legitimate vendor email accounts to submit altered invoices or request payment changes. Because these requests appear to come from trusted partners, they can move through routine approval processes without immediate concern.
5. Recurring Billing Abuse
Subscription-based billing models can create opportunities for recurring invoices tied to services that are no longer active or required. Without periodic review of recurring vendor payments, these charges may persist unnoticed over time.
6. Insider Invoice Fraud
Insider fraud occurs when employees manipulate invoice creation or approval processes for personal gain. This risk increases in environments where financial responsibilities are not clearly separated or approval controls are inconsistently applied. (To see what this tactic looks like in real-life, read more Macy’s $154M incident).
Why Invoice Fraud Persists Despite Existing Controls
Most organizations already maintain financial safeguards such as approval workflows, invoice matching, and periodic audits. These controls are designed to validate transactions, not to detect manipulation within otherwise legitimate workflows.
This is where modern invoice fraud succeeds.
When a request includes expected documentation, aligns with vendor relationships, and follows normal processes, it moves forward—not because it is verified, but because it appears complete.
When Everything Checks Out
When invoice fraud is discovered, the first reaction is often confusion. From a process standpoint, everything appears to check out. The invoice matches a purchase order, the vendor is recognized, and even bank account validation may be completed.
This is because most process controls are designed to confirm that a transaction aligns with existing records—not to question whether the request itself is legitimate.
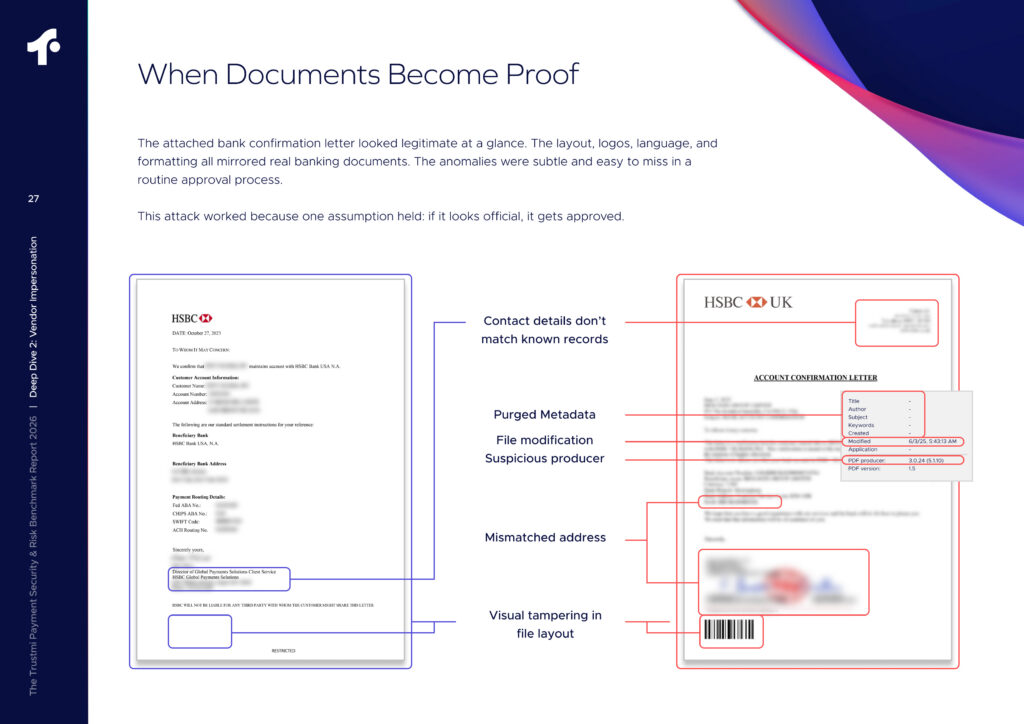
When Documents Become Proof
Financial documents are often treated as static records to be reviewed and approved. But in practice, they are increasingly used as active components of fraud—designed to validate and reinforce payment requests rather than simply support them.
For example, an invoice may match a purchase order and pass standard approval checks, while the payment instructions associated with that invoice have been altered. Similarly, requests that appear to come from trusted vendors may move through routine communication channels without raising concern.
Because these schemes exploit trust within established vendor relationships, fraudulent invoices can move through accounts payable processes without triggering traditional controls.
What’s at Stake When Invoice Fraud Occurs
For accounts payable teams, invoice fraud is rarely limited to a single incorrect payment. When fraudulent invoices pass through payment workflows, the consequences often extend beyond the initial transaction.
Financial Exposure
The most immediate impact is unauthorized payments leaving the organization. In high-volume AP environments, even small discrepancies can escalate quickly—particularly when duplicate invoices, inflated charges, or manipulated payment instructions move through routine workflows.
Beyond the direct loss, finance teams often spend significant time investigating transactions, reconciling vendor accounts, and correcting financial records. What begins as a single fraudulent payment can quickly become a broader operational disruption.
Audit and Compliance Pressure
Fraud incidents often trigger deeper scrutiny of financial controls. Finance leaders may need to review payment processes, explain the incident to auditors, and demonstrate that appropriate safeguards are in place.
Even a single incident can raise questions about whether existing payment controls adequately protect vendor transactions.
Vendor and Internal Trust
Fraudulent payments can also strain vendor relationships. This is particularly the case when legitimate invoices go unpaid or payments are redirected to fraudulent accounts. Internally, these incidents often draw increased attention from finance leadership, risk teams, and executive stakeholders responsible for safeguarding company funds.
Key Controls That Help Prevent Invoice Fraud
Organizations rely on multiple layers of control to reduce invoice fraud risk, including vendor validation, approval workflows, payment verification, and visibility into vendor and payment activity.
These controls form the foundation of strong accounts payable operations and play a critical role in reducing exposure.
However, as payment processes accelerate and vendor ecosystems grow, maintaining these controls manually becomes more difficult. At the same time, attackers are designing requests that align with expected processes, making fraudulent activity harder to distinguish from legitimate transactions.
To keep pace, many organizations are augmenting these controls with AI-driven analysis to evaluate patterns, context, and anomalies across payment activity at scale.
Vendor Due Diligence
Validating vendor identities before onboarding helps prevent unauthorized vendors from entering payment workflows. Many organizations verify vendor credentials, tax information, and payment details before allowing vendors to submit invoices.
Segregation of Duties
Separating invoice approval, verification, and payment authorization responsibilities helps reduce the risk of both internal manipulation and unauthorized transactions within payment processes.
Verification Procedures
Matching invoices against purchase orders, contracts, and delivery confirmations helps ensure that payments correspond to legitimate business transactions. Consistent validation procedures help reduce the likelihood that inaccurate or manipulated invoices are approved.
Periodic Audits and Reviews
Regular reviews of invoice activity, vendor payments, and contract terms help finance teams reinforce internal controls and identify inconsistencies within vendor relationships.
Employee Awareness
Employees involved in invoice processing should remain aware of common fraud schemes that target vendor payments. Awareness helps ensure that unusual payment requests or vendor communications receive appropriate scrutiny.
Technology and Payment Visibility
Many organizations supplement traditional financial controls with technology that provides visibility into vendor activity, payment patterns, and invoice workflows. These systems help finance teams monitor payment processes and reduce the likelihood of unauthorized transactions.
Secure Financial Systems
Protecting financial systems and vendor communication channels through access controls, authentication safeguards, and system security practices helps reduce the risk of compromised accounts and manipulated payment requests.
Vendor Relationship Oversight
Maintaining clear vendor communication channels and periodically reviewing vendor payment details helps organizations ensure that vendor information remains accurate and consistent across payment systems.
Safeguarding Vendor Payments from Invoice Fraud
As payment workflows become more complex, reducing exposure to invoice fraud requires more than traditional controls. It requires visibility into how vendor payments behave across systems and over time.
Most organizations already validate invoices against purchase orders, verify vendors, and follow structured approval processes. But as this analysis shows, these checks are not designed to detect fraud that appears legitimate within those same workflows.
When a request includes expected documentation and follows established processes, it moves forward. This is why invoice fraud continues to succeed. It does not rely on breaking controls. It relies on operating within them.
Reducing risk requires more than verifying individual steps. It requires understanding how payment requests behave across systems and over time. And organizations that strengthen this visibility are better positioned to identify inconsistencies within otherwise routine transactions.
To learn how fraud teams are applying this approach in practice, explore our guide to identifying fake invoices before payments are approved.










 Behavioral AI-powered security
Behavioral AI-powered security Protection on day one
Protection on day one 10-15x ROI
10-15x ROI